rewrite this content using a minimum of 1200 words and keep HTML tags
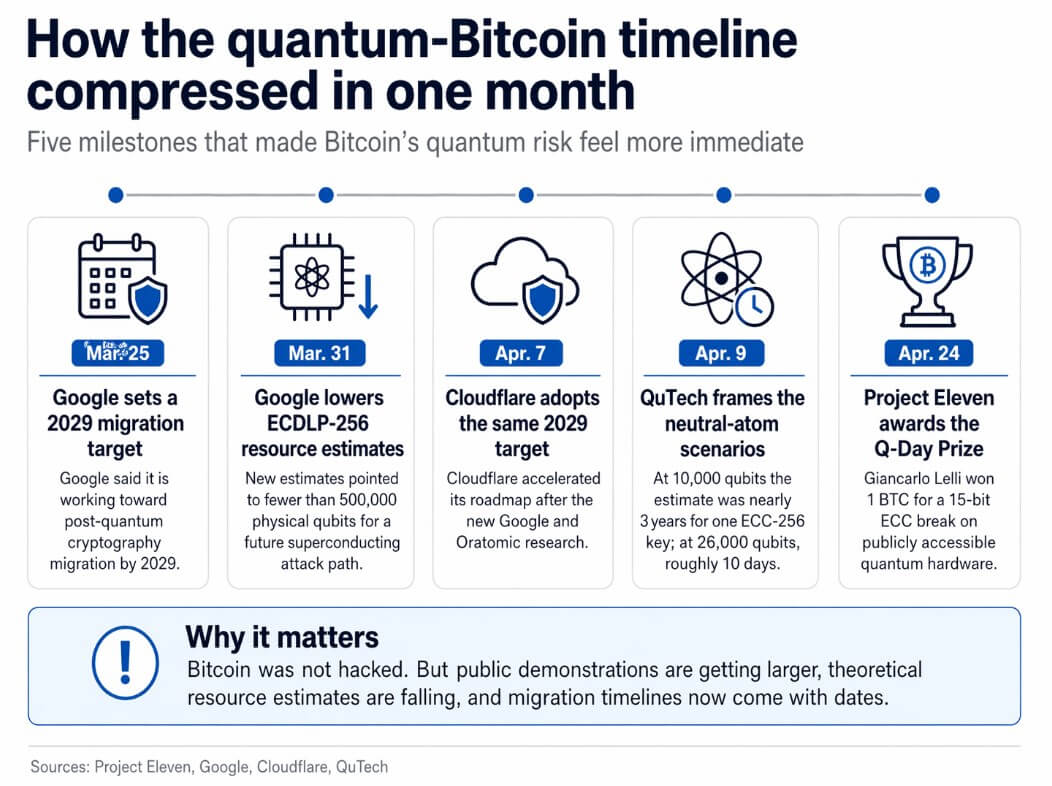
On Apr. 24, Project Eleven awarded its Q-Day Prize to Giancarlo Lelli, a researcher who used publicly accessible quantum hardware to derive a 15-bit elliptic curve private key from its public key.
This is the largest public demonstration to date of the attack class that could one day threaten Bitcoin, Ethereum, and every other system secured by elliptic curve cryptography. The prize was one Bitcoin.
The irony is that a researcher won Bitcoin by breaking a miniature version of the math that protects Bitcoin.
A 15-bit key is nowhere near the security of Bitcoin’s 256-bit elliptic curve, and no publicly known quantum computer can break real Bitcoin wallets today.
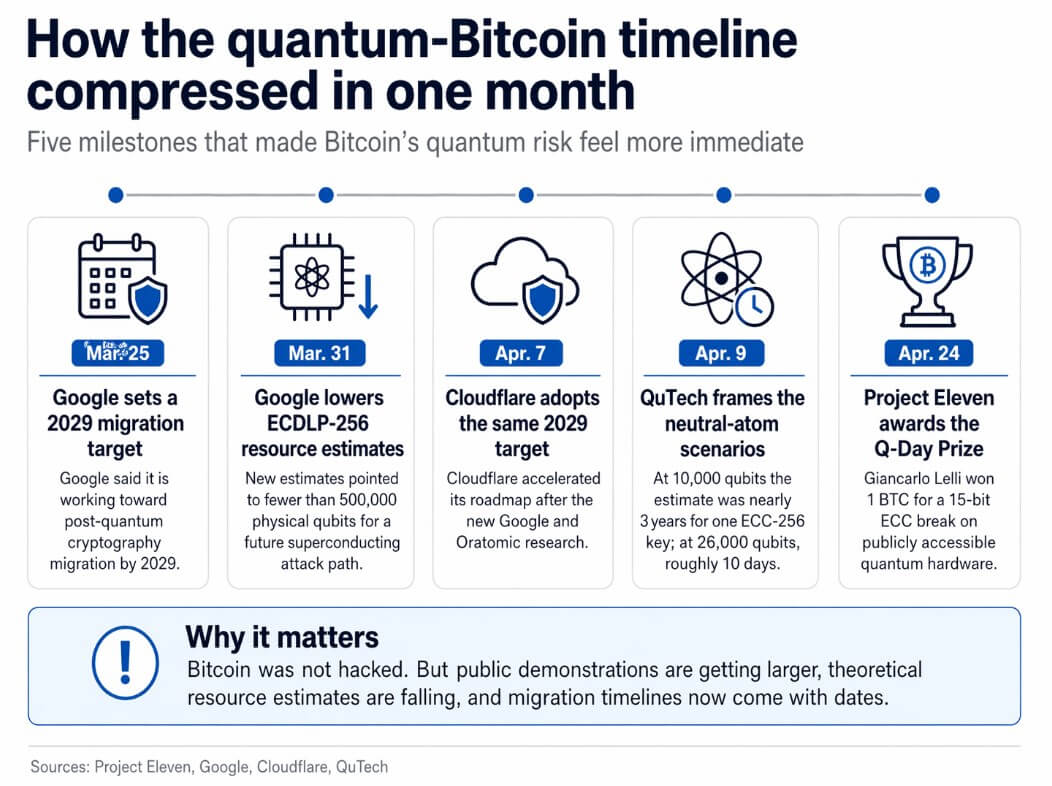
The result arrives at a moment when the surrounding context has gotten considerably more serious, with Google cutting its ECDLP-256 resource estimates and setting a 2029 migration deadline in the same month.
What Lelli actually did
Lelli used a variant of Shor’s algorithm, a quantum algorithm targeting the elliptic-curve discrete logarithm problem, the mathematical foundation of Bitcoin’s signature scheme, to recover a private key from a public key over a search space of 32,767.
The Q-Day Prize competition asked entrants to break the largest possible ECC key on a quantum computer, with no classical shortcuts or hybrid tricks.
Lelli’s 15-bit result was the highest any entrant reached by the deadline, and Project Eleven described it as a 512x jump over Steve Tippeconnic’s 6-bit September 2025 demonstration.
The winning machine had roughly 70 qubits, per Decrypt’s reporting, and an independent panel including researchers from the University of Wisconsin-Madison and qBraid reviewed the submission, according to Project Eleven.
The right frame for this result is a toy lock picked using the same family of methods that would one day threaten the vault. The locksmiths improved, and the vault holds for now.
ClaimWhat the article supportsWhy it mattersA quantum computer broke a 15-bit ECC keyProject Eleven says Giancarlo Lelli derived a 15-bit elliptic curve private key from its public key using publicly accessible quantum hardwareIt turns the quantum threat into a concrete public demonstration rather than a purely theoretical warningBitcoin itself was not hackedThe article explicitly says no publicly known quantum computer can break real Bitcoin wallets todayThis keeps the piece credible and avoids overstating the resultThe result used the same attack family relevant to BitcoinLelli used a variant of Shor’s algorithm targeting the elliptic-curve discrete logarithm problem, which underlies Bitcoin’s signature schemeIt connects the toy demo to the real cryptographic risk without claiming equivalenceThe demo was done under constrained rulesThe Q-Day Prize required entrants to break the largest possible ECC key on a quantum computer with no classical shortcuts or hybrid tricksIt strengthens the significance of the result as a quantum benchmarkThe result is larger than prior public ECC demonstrationsProject Eleven described the 15-bit result as a 512x jump over Steve Tippeconnic’s 6-bit September 2025 demonstrationIt shows the public demo frontier is advancingThe gap to Bitcoin’s 256-bit security remains enormousThe article notes that a 15-bit key is nowhere near Bitcoin’s 256-bit elliptic curve securityThis is the central caveat readers need in order to interpret the story correctlyThe hardware was still small by real-attack standardsThe winning machine reportedly had roughly 70 qubitsIt underlines that the achievement is meaningful as a milestone, not as proof that full-scale attacks are imminentThe real story is directional, not catastrophicPublic demos are getting bigger, resource estimates are falling, and migration deadlines now have concrete datesThe threat is still future tense, but the timeline is getting harder to dismiss
The reason this demo lands with more weight than it would have six months ago is Google.
On Mar. 31, Google published new ECDLP-256 resource estimates for circuits using fewer than 1,200 logical qubits and 90 million Toffoli gates, or fewer than 1,450 logical qubits and 70 million Toffoli gates.
Google estimated those circuits could execute on a superconducting cryptographically relevant quantum computer with fewer than 500,000 physical qubits, roughly a 20-fold reduction from prior estimates.
On Mar. 25, Google set a 2029 target for its own post-quantum cryptography migration, tying the deadline explicitly to progress in hardware, error correction, and resource estimates.
Cloudflare matched that 2029 target on Apr. 7, citing both the Google paper and a Caltech/Oratomic preprint as reasons for acceleration.
That preprint argued that neutral-atom architectures could run Shor’s algorithm at cryptographically relevant scales with as few as 10,000 reconfigurable atomic qubits.
Commenting on Apr. 9, QuTech noted that at 10,000 qubits, the architecture would still require nearly three years to break a single ECC-256 key, while the more time-efficient 26,000-qubit configuration would bring the runtime to roughly 10 days.
Both estimates depend on machines that do not yet exist, and the Caltech/Oratomic work is an unreviewed preprint.
The useful takeaway from those numbers is that some theoretical architectures now place the long-term hardware requirement far below what researchers assumed a year ago.
The clocks for public demonstrations are getting shorter, resource estimates are falling, and migration timelines now carry concrete dates.
Bitcoin wallets are already exposed
Project Eleven’s live tracker currently lists 6,934,064 BTC as vulnerable to a quantum attack.
The vulnerability is that quantum attacks are most dangerous when a public key is already visible on-chain, which happens with older address types, reused addresses, and partial spends.
Some Bitcoin wallets have already exposed their public keys through prior transactions. Google’s Mar. 31 paper sharpened that picture, noting that fast-clock cryptographically relevant quantum computers could enable on-spend attacks on public mempool transactions, extending the risk from dormant old wallets to live spending.
Bitcoin’s governance has begun to respond with BIP 360, which proposes a new output type removing Taproot’s quantum-vulnerable key-path spend. BIP 361 proposes a phased sunset of legacy signatures that would push quantum-vulnerable outputs toward migration.
Their existence confirms that Bitcoin has entered the migration phase. The harder problem ahead is if a decentralized network can align on incentives, timetables, and the treatment of dormant or lost coins before urgency outruns coordination.
Two paths forward
In the bull case, migration becomes routine before any emergency arrives.
Google’s and Cloudflare’s 2029 targets reset expectations across the industry, wallet providers and exchanges push users away from long-exposure address patterns, and Bitcoin governance coalesces around output changes before any real cryptographically relevant quantum computer materializes.
Q-Day stays future tense, and the most vulnerable stock of BTC tied to exposed public keys shrinks as hardware catches up.
In the bear case, the attack path keeps looking more like engineering than science fiction, outpacing governance’s response.
More public key break demonstrations arrive, architecture-specific estimates fall again, and the market starts repricing vulnerable UTXOs and long-idle coins.
The damage in this scenario begins with the erosion of confidence, governance conflict, and rushed migration planning under the clock. A decentralized network with no central authority to mandate deadlines faces the hardest version of that race.
ScenarioWhat changesWhat stays vulnerableMarket / governance implicationBull caseMigration becomes routine before any emergency arrives; wallet providers, exchanges, and protocol developers begin reducing public-key exposureOlder address types, reused addresses, and some dormant wallets still carry risk until fully migratedConfidence holds because the ecosystem treats quantum risk as an infrastructure upgrade rather than a crisisBear casePublic key-break demonstrations keep improving and hardware/resource estimates keep falling faster than governance adaptsExposed public keys, long-idle coins, partial spends, and live-spend transactions remain exposed for longerMarkets begin repricing vulnerable UTXOs, governance conflict intensifies, and migration happens under pressureWhat reduces risk fastestBetter wallet hygiene, fewer reused addresses, reduced public-key exposure, adoption of new output types, and phased retirement of legacy signaturesCoordination problems remain, especially around lost coins and slow-moving usersThe network buys time and lowers the number of coins exposed before cryptographically relevant quantum machines existWhat raises urgency fastestLarger public demos, lower hardware estimates, faster-clock architectures, and stronger evidence that on-spend or mempool attacks could become practicalAny wallet whose public key is already visible becomes more sensitive to future advancesThe debate shifts from “should we prepare?” to “how fast can Bitcoin coordinate?”Key external deadlinesGoogle and Cloudflare target 2029; the UK’s NCSC sets milestones at 2028, 2031, and 2035Decentralized crypto networks cannot move as quickly as centralized firms by defaultBitcoin faces a harder version of the migration race because it depends on distributed coordination rather than a single authorityBottom-line consequenceIn the best case, Q-Day stays future tense long enough for migration to get ahead of the threatIn the worst case, technical progress outpaces social and governance responseThe real risk is not only eventual key-breaking power, but whether the ecosystem can align before urgency outruns coordination
The UK’s National Cyber Security Center has set migration milestones at 2028, 2031, and 2035. Google and Cloudflare both target 2029.
The Ethereum Foundation says migrating a global decentralized protocol takes years and must begin before the threat arrives.
Bitcoin’s quantum threat now lives in public demonstrations, corporate migration calendars, and draft protocol proposals.
and include conclusion section that’s entertaining to read. do not include the title. Add a hyperlink to this website http://defi-daily.com and label it “DeFi Daily News” for more trending news articles like this
Source link