rewrite this content using a minimum of 1000 words and keep HTML tags
AI agents could end the app era by turning software into verified, user-built systems
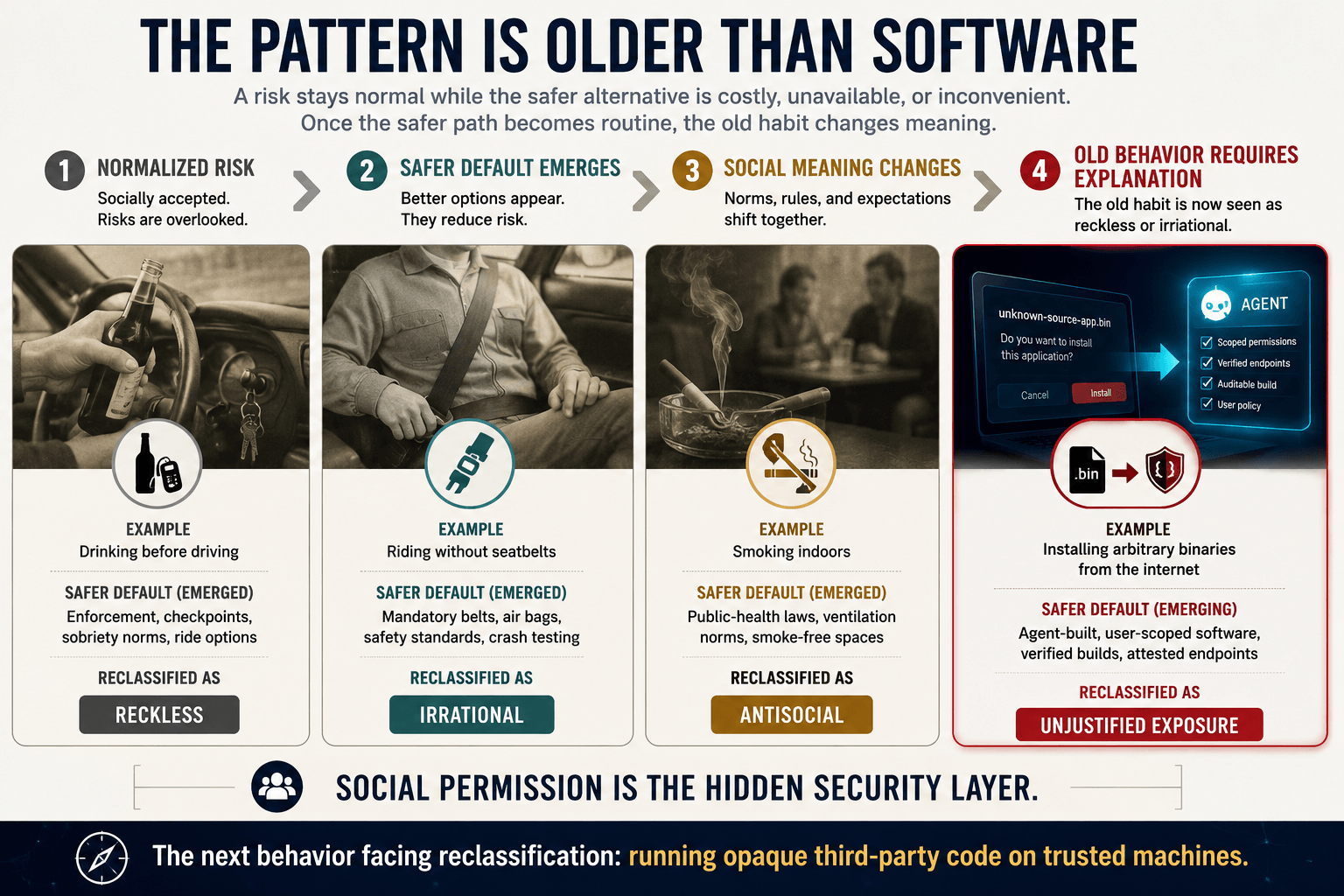
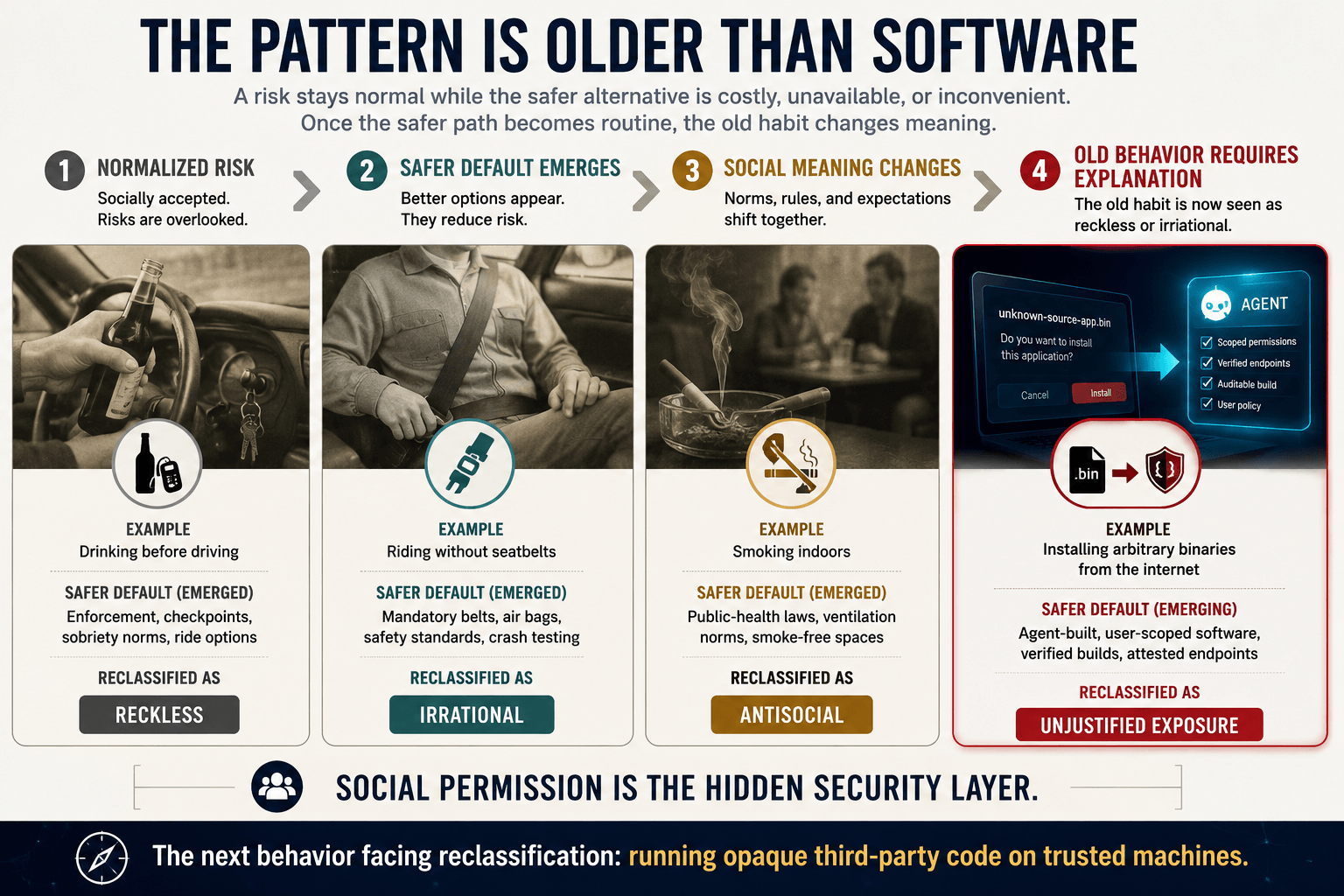
AI agents may make running code written by strangers one of those behaviors that later generations struggle to process.
A society can normalize a risk for decades, then later reclassify it as reckless once a safer default becomes available.
Drinking before driving, riding without seatbelts, smoking indoors, and installing arbitrary binaries from the internet all belong to the same family of historical blind spots. The common feature is social permission.
The behavior persists when the alternative is costly, inconvenient, or technically unavailable. Once the safer path becomes cheap and routine, the old path begins to look irrational.
AI agents expose the weakness in the software trust model
Modern software still runs on a bargain that we rarely inspect. A developer, company, foundation, or anonymous maintainer writes code. A distribution channel packages it. A user, enterprise, or operating system runs it.
Security then becomes a layered attempt to manage the consequences of that decision.
Permissions, code signing, app stores, endpoint detection, sandboxing, vendor due diligence, and incident response all exist because the core act remains dangerous: executing someone else’s instructions on your machine, inside your account, with access to your data.
That trust model has failed at the institutional scale. The SolarWinds compromise showed how malicious code inserted into a trusted software build process could be distributed through normal updates and reach government agencies, technology firms, telecom networks, and other targets across multiple regions.
The operational lesson was structural, and the attack surface was the vendor’s legitimacy itself.
Once the build process was compromised, the normal marks of trust became delivery infrastructure for the attack.
The same pattern appeared in the XZ Utils backdoor, where CISA warned in March 2024 that malicious code had been embedded in versions 5.6.0 and 5.6.1 of a compression library present across Linux distributions.
The National Vulnerability Database later described how a disguised test file and build-process manipulation produced a modified liblzma library capable of intercepting and modifying data interactions in linked software.
A software supply chain can be compromised far upstream from the user, and then arrive through channels that appear routine. We’ve seen that in crypto countless times with DNS and JavaScript npm exploits.
The industry response has been to add a stronger process. The NIST Secure Software Development Framework gives organizations a common set of practices for building and acquiring software with reduced risk.
The SLSA framework pushes provenance, integrity, and tamper resistance into the artifact pipeline. These controls are necessary.
They also reveal the limit of the present model. Enterprises keep refining methods for deciding which external code deserves trust.
The next model reduces the amount of outside code that needs trust at all.
That shift changes the social meaning of software. Today, third-party code is treated as a productivity asset with security overhead.
Tomorrow, it may be treated as a liability that requires justification. The default user question moves from “Which app should I install?” to “Why should I run someone else’s app when my agent can build the function for me?”
That is a real fracture line. Software stops being primarily a product selected from a market and becomes an output generated on demand within a user-controlled execution environment.
Agent-built software turns apps into disposable expressions of intent
The direction of travel is visible in coding agents. OpenAI Codex was introduced as a cloud-based software engineering agent capable of working on multiple tasks in parallel.
Claude Code by Anthropic is an agentic coding system that maps a codebase, changes files, runs tests, and delivers committed code.
GitHub’s Copilot coding agent moved the same pattern into the GitHub workflow, with asynchronous work across issues and pull requests.
Google Jules presents a similar direction: an autonomous coding agent that absorbs product context, generates solutions, and ships pull requests.
These products are still framed as developer tools. That framing will narrow over time. For Codex, it already is. OpenAI introduced a UI option last month focused on ‘chats’ and outputs rather than on code and terminals.
The bigger change is that software creation is becoming a personal act of delegation. A user describes a workflow. The agent generates the interface, logic, integrations, tests, and execution path.
The artifact may last for an hour, a week, or a year. It can be regenerated, forked, constrained, audited, discarded, or rebuilt for a new context.
The app becomes less like a permanent object and more like a local policy compiled into a usable interface.
That has immediate implications for trust. A user may still observe other people’s applications. They may inspect workflows, interface patterns, data schemas, prompts, automations, and service integrations. Yet observation can remain separate from execution.
The user can copy the idea, then ask a personal agent to rebuild the function from first principles inside an environment governed by that user’s own rules. The value migrates from the compiled artifact to the pattern.
Distribution becomes less about shipping executable code and more about publishing intent, design, proofs, schemas, and API expectations.
Crypto enters the argument through verification rather than branding. The user’s agent will still connect to outside services.
It may call payments rails, identity systems, market data endpoints, storage layers, AI model providers, compute markets, messaging systems, and compliance services. The trust boundary shifts to those endpoints and the claims made about them.
Users will need ways to rank external services by auditability, provenance, security posture, and economic alignment. A service built within a verifiable environment will be scored differently from a black-box endpoint controlled by a corporate platform.
Verifiable endpoints become the new software distribution layer
Zero-knowledge systems provide one path into that ranking layer. ZK rollups show how computation can be executed off-chain while a succinct proof verifies the validity of the resulting state transition on-chain.
The same conceptual pattern can extend beyond transaction scaling. Users may want proofs that an endpoint ran approved code, processed data under defined constraints, preserved privacy boundaries, or produced a result from a specific audited build.
The proof can preserve internal confidentiality while narrowing the trust gap between a personal agent and an external dependency.
The long-term interface may resemble an agent-controlled operating layer. The user asks for a dashboard, a portfolio tool, a research assistant, a publishing system, a personal CRM, an accounting workflow, or a security monitor.
The agent assembles it from generated code and ranked endpoints. The code is inspectable because the agent created it.
The dependencies are constrained because the agent selected them under policy. The execution environment is auditable because the user chose that as a requirement.
The user still participates in a networked economy. Control moves closer to the individual.
The endpoint of this transition is a market for verifiable functions, agent-generated clients, and ranked external services. Third-party developers still exist, yet their role changes.
They publish protocols, APIs, templates, proofs, models, components, and reference implementations. Users run their own versions.
Enterprises still exist, yet their advantage shifts from controlling distribution to proving reliability. Open-source communities still exist, yet the burden moves from asking users to trust maintainers toward giving agents enough structured material to rebuild safely.
The old software economy sold finished applications. The new one sells credible capabilities.
A portfolio tracker becomes a generated interface over market data endpoints, wallet permissions, tax logic, and reporting rules. A publishing system becomes a generated workflow over identity, editing, content management, analytics, and distribution APIs.
A research terminal becomes a surface generated from databases, model calls, provenance checks, and private notes. In each case, the user’s agent handles composition.
The external world provides verifiable resources. That change also creates a commercial test for every infrastructure provider: prove the claim, publish the interface, expose the constraint set, and let user-side agents decide whether the service deserves inclusion.
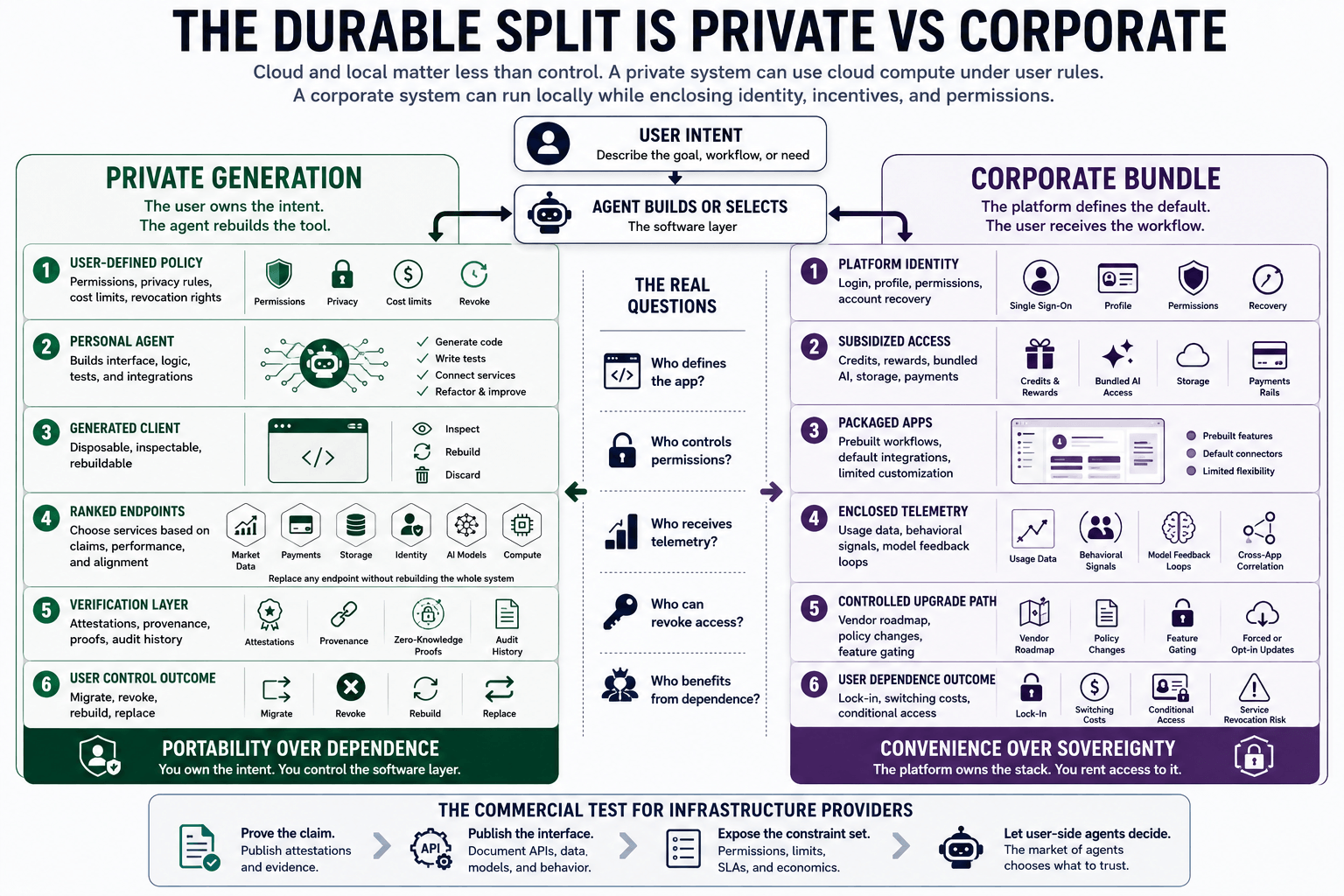
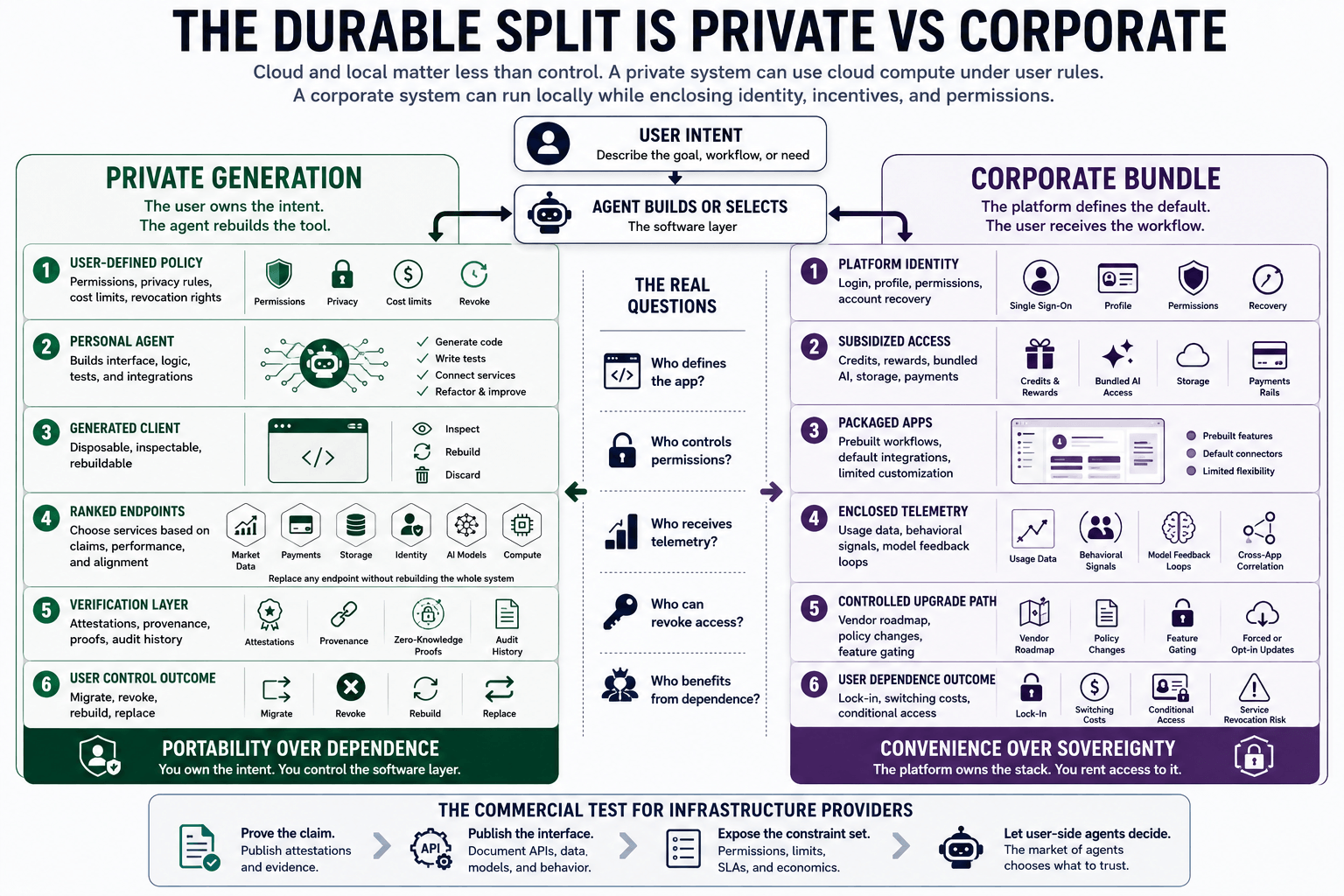
The central split becomes private software sovereignty versus managed convenience
The usual debate frames the future as local versus cloud. That division captures part of the infrastructure question, while missing the political economy.
A private system can use cloud compute under user-defined constraints. A corporate system can run locally while still enclosing identity, incentives, permissions, and monetization inside a vendor-controlled stack.
The more durable split is private versus corporate. Who defines the app?
Who decides what it can access? Who receives the telemetry?
Who sets the upgrade path? Who can revoke the function?
Who benefits from the user’s dependence?
That split will become more visible as agentic software becomes cheap enough for ordinary users. One path leads toward personal software sovereignty.
Users maintain agents that build and rebuild the tools they need. They choose endpoint providers based on attestations, cost, reliability, privacy, and alignment.
They can abandon an interface while preserving the underlying workflow. They can migrate from one endpoint to another.
They can generate a new client when an old one becomes compromised, captured, or inefficient. The software layer becomes portable because the user owns the intent, and the agent can reproduce the implementation.
The other path leads toward managed convenience. Corporate platforms will offer subsidized apps, integrated identity, credits, payments, storage, AI access, and default workflows.
Some of that will be useful. Some of it will be economically coercive.
If AI-driven abundance produces public or private UBI-adjacent income schemes, compute credits, token distributions, or platform-linked benefits, the distribution rail may become a soft lock-in mechanism. Users may receive access to services through an ecosystem that also defines what software they run, how their data moves, and which agents can act on their behalf.
The UBI layer is the most sensitive version of that problem. Sam Altman has long been associated with AI-era debates over income distribution, and Worldcoin was framed, in part, around proof of personhood and the possibility of UBI-like distributions.
The broader point is larger than one project. When economic support, identity verification, compute access, and software permissions converge, participation can become conditional while looking voluntary.
A user may be free to opt out in theory while being pushed toward a managed application layer in practice.
Convenience becomes the main battleground. The corporate stack will win users through low friction.
It will offer polished defaults, instant access, bundled AI, social compatibility, recovery flows, compliance coverage, and rewards. The private stack will need to compete on something harder: autonomy that feels usable.
It must give users a reason to accept more responsibility while avoiding technical administration. The personal agent becomes decisive because it can absorb the complexity that previously made sovereignty impractical.
The next test is whether users choose generated trust over packaged convenience
The first-order risk is that users trade control for convenience before they understand the cost. The second-order risk is that the trade becomes subsidized, normalized, and eventually required for access to economic life.
Corporate apps may become the default environment for those who accept bundled benefits. Privately generated apps may become the default for those willing to pay, verify, configure, or self-custody their software layer.
That creates a new class divide around execution control. The question is whether agentic AI compresses that divide or deepens it.
That transition will be uneven. Regulated sectors will move slower.
Enterprises will defend app ecosystems with compliance arguments. Consumers will continue to choose default convenience when the private alternative feels brittle.
Attackers will target agents, prompts, dependency selection, model supply chains, and endpoint attestations. Verification systems will create new chokepoints if they become captured by a small number of certificate authorities, cloud platforms, or model vendors.
Personal software sovereignty can become another brand claim unless users can inspect, migrate, and revoke.
Still, the direction is clear enough to define the next test. The question is whether people will accept convenience over sovereignty once their own agents can build most of what they need.
Today, the answer is largely yes because the alternative remains too demanding. Tomorrow, the answer becomes less certain.
A user who can generate a working app, constrain its permissions, audit its dependencies, connect only to ranked endpoints, and rebuild it when conditions change has a real alternative to the corporate software bundle.
That alternative will feel strange at first. Then it will feel prudent.
Then it may become the default expectation for anyone handling money, identity, health data, private communications, research, or business operations. Running opaque third-party code will survive when convenience dominates, when subsidies distort choice, and when users accept managed environments in exchange for economic access.
It will fade where agents make private generation routine.
The social reclassification will happen slowly, then suddenly. The old habit will remain familiar until the new default becomes obvious.
Once users can ask their own agents to build the application, verify the execution path, and connect only to attested endpoints, the burden of explanation flips. The person running someone else’s code will need a reason.
The person building through an agent will simply be using the safer default. However, they may also have to accept missing out on corporate incentives given to those who remain connected to the matrix.
and include conclusion section that’s entertaining to read. do not include the title. Add a hyperlink to this website http://defi-daily.com and label it “DeFi Daily News” for more trending news articles like this
Source link